‘XDR’: Re-evaluating Detection Efficiency in Threat Detection & Response
by Noa Glumcher
Sep 9, 20192019 is witnessing a wave of “awakening” in cybersecurity Threat Detection and Response (‘TDR’). The domain has gained greater interest in recent years when organizations determined “Prevention” was no longer enough. Until recently, it consisted of three main solution categories:
- Single-sensor security solutions: Mainly Endpoint Detection and Response or Endpoint Protection Platform (EDR/EPP). Some also consider Network Traffic Analysis (NTA) solutions under this category;
- Managed security solutions: Managed Detection and Response (MDR) and Managed Security Service Provider (MSSP), ranging in the level of response they provide;
- Data management solutions, that better organize, visualize, and serve organizations’ data. Mainly, these are Security Information and Event Management (SIEM) platforms.
A New Chapter in Threat Detection & Response
Since the beginning of 2019, however, we are seeing a shift in the way organizations and vendors address threat detection efficiency, which might bring about a new category. Specifically, security vendors are attempting to improve: allocation of data sources, threat telemetry and analytics delivery, and the accessibility of cyber-adversary expertise (that is why the MITRE ATT&CK framework has gained tremendous traction lately).
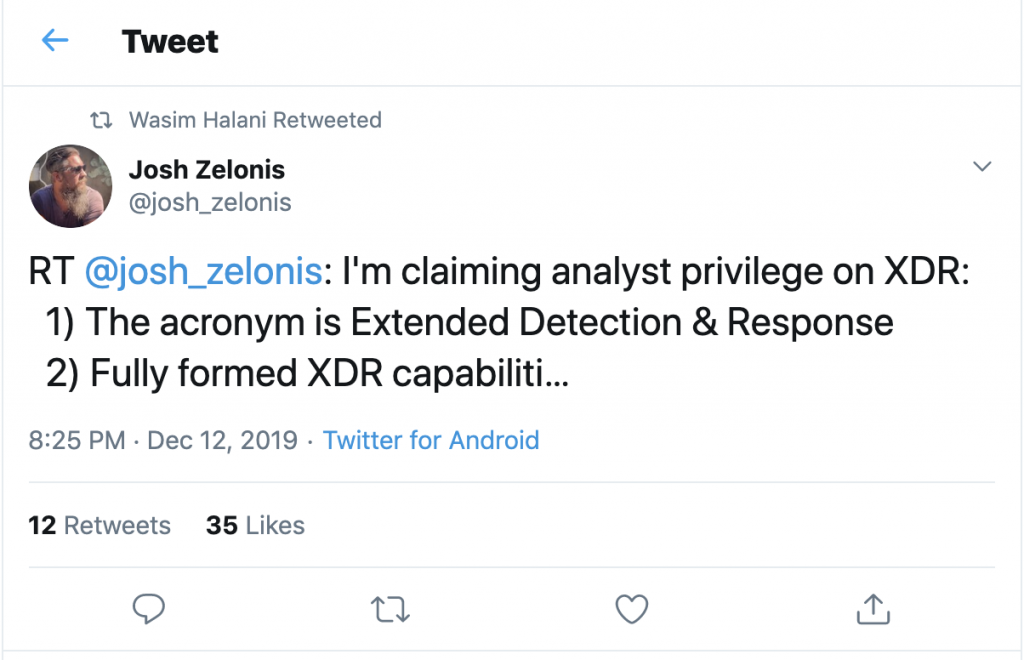
Aligning with this mind shift, cybersecurity analysts are now trying to name a new and improved category for threat detection and response. Currently dubbed ‘EDR+’, or ‘XDR’, this new TDR category aims to move beyond endpoint/single-sensor level, and can be affiliated with two main enhancements:
- CONSOLIDATION of data sources. New solutions are expanding their data sources (platforms, logs, events) to gain a broader view of the environment and enable organizations to better tackle the growth in attack surfaces and in the sophistication of threats. A good case in point would be Palo Alto Networks’ and Trend Micro’s recently-launched ‘XDR’ solutions – these expand detection beyond the endpoint. Google and Microsoft are also consolidating technologies, pushing telemetry beyond endpoint level on Google Cloud Platform and Microsoft Azure products.
- AUTOMATION of processes. A recent ESG research found two of the five top challenges for threat detection and response to deal with the human factor (these were: Hindrance caused by manual processes and the shortage in cyber-adversary expertise). While SOC processes are likely to remain analyst-centric, CISOs and SOC teams have started looking closer into self-sufficient, effective detection and response tools. These should also enable less friction with noise.
 |
 |
Is EDR Dead? What is 'XDR'?
The EDR market is undergoing changes. Forrester’s Josh Zelonis went so far as to describe VMware’s acquisition of Carbon Black as “signaling the end of ‘Endpoint’ Detection and Response”. Is this really it? According to Gartner, not quite yet. We can expect, however, to see EDR merge into EPP, with greater emphasis on incident response.
Regardless of the case of EDR, organizations and vendors are increasingly looking to improve threat detection and response capabilities. ‘XDR’ would be the latest and greatest to support this notion, representing solutions that push the envelope beyond endpoint level, correlating multiple data sources, and automating these processes on the go.
But vendors who offer vendor-specific ‘XDR’ can only push so far. They have expanded data correlation beyond the endpoint, but have stayed within their own perimeters. An effective ‘XDR’ solution should be able to correlate events and log data from every data source, platform, and device in a vendor-agnostic manner to proactively detect threats and provide a full analysis of attack story. When highly effective, it should also allow you to utilize your existing security controls, for holistic, spot-on detection.
Four Questions to ask yourself when Evaluating Threat Detection & Response Tools
If you are looking to boost your TDR game while drastically improving threat detection efficiency, be sure to ask examined vendors the following questions:
- How many platforms do you cover? Cloud/Endpoint/Network/All? Do you look at them separately all together? (Ok, this might have been a three-in-one sort of question). The answer will provide a good indication of the number of attack surfaces covered
- How autonomous can you be? SOC teams are drowning in a sea of noise. You’re looking for a solution that is as autonomous as it can be, one that lets your SOC team deliver easily and rapidly
- Will your threat detection put me in a vendor lock? Choose a solution that allows you to utilize protection tools that best fit your business
- Do they have the right cyber domain expertise? Understanding cyber attack surfaces, signatures, behaviors, and anomalies is not enough. Look for a solution that brings overarching cyber-adversary expertise in order to tackle the disease, not its symptoms.
In other words: look for a solution that allows you to stop looking for threats and actually starts finding them instead.
Learn more about Hunters' open XDR.